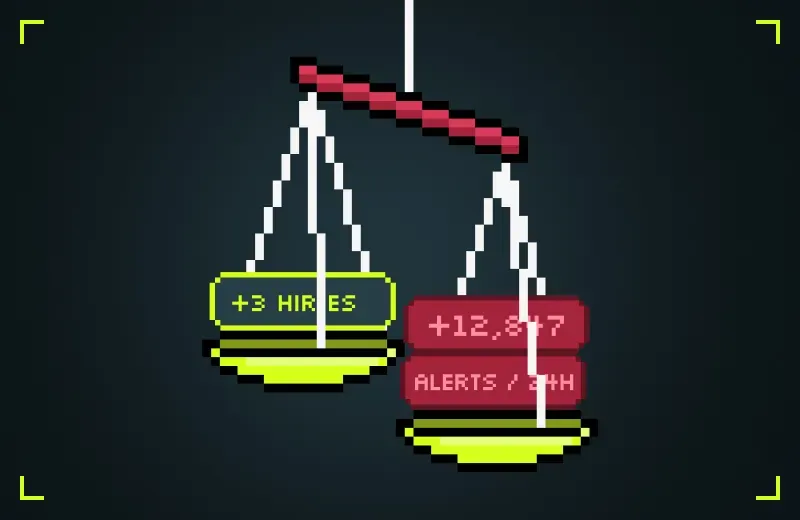
Hire More People
Skilled security talent is expensive, scarce, and takes time to ramp. Headcount can't scale as fast as threats, and every new hire multiplies onboarding overhead.
- Talent supply can't keep pace with alert volume.
- Ramp times stretch weeks before first value.
- Linear cost model against exponential threat surface.